标签归档:渗透测试
渗透测试人员的Python工具箱
如果你从事的行业是漏洞研究,逆向工程或者渗透测试,那么Python语言你将值得拥有。它是一个具有丰富的扩展库和项目的编程语言。本文仅仅列出了其中的一小部分。下面列举的工具大部分是用Python写的,剩下的一部分是C语言库的Python实现,且他们很容易被Python所使用。其中有些有攻击性比较强的工具(如:渗透测试框架,蓝牙,web漏洞扫描器,等等)被遗漏了,因为这些工具的使用在德国仍然存在一些法律风险。
网络:
-
Scapy, Scapy3k: send, sniff and dissect
and forge network packets. Usable interactively or as a library -
pypcap, Pcapy and pylibpcap: several different
Python bindings for libpcap -
libdnet: low-level networking
routines, including interface lookup and Ethernet frame transmission -
dpkt: fast, simple packet
creation/parsing, with definitions for the basic TCP/IP protocols -
Impacket:
craft and decode network packets. Includes support for higher-level
protocols such as NMB and SMB -
pynids: libnids wrapper offering
sniffing, IP defragmentation, TCP stream reassembly and port scan
detection -
Dirtbags py-pcap: read pcap
files without libpcap -
flowgrep: grep through
packet payloads using regular expressions -
Knock Subdomain Scan, enumerate
subdomains on a target domain through a wordlist -
SubBrute, fast subdomain
enumeration tool -
Mallory, extensible
TCP/UDP man-in-the-middle proxy, supports modifying non-standard
protocols on the fly -
Pytbull: flexible IDS/IPS testing
framework (shipped with more than 300 tests)
调试与逆向工程:
-
Paimei: reverse engineering
framework, includes PyDBG, PIDA,
pGRAPH -
Immunity Debugger:
scriptable GUI and command line debugger -
mona.py:
PyCommand for Immunity Debugger that replaces and improves on
pvefindaddr -
IDAPython: IDA Pro plugin that
integrates the Python programming language, allowing scripts to run
in IDA Pro -
PyEMU: fully scriptable IA-32
emulator, useful for malware analysis -
pefile: read and work with
Portable Executable (aka PE) files -
pydasm:
Python interface to the libdasm x86 disassembling library -
PyDbgEng: Python wrapper for the
Microsoft Windows Debugging Engine -
uhooker:
intercept calls to API calls inside DLLs, and also arbitrary
addresses within the executable file in memory -
diStorm: disassembler library
for AMD64, licensed under the BSD license -
python-ptrace:
debugger using ptrace (Linux, BSD and Darwin system call to trace
processes) written in Python -
vdb / vtrace: vtrace is a
cross-platform process debugging API implemented in python, and vdb
is a debugger which uses it -
Androguard: reverse
engineering and analysis of Android applications -
Capstone: lightweight
multi-platform, multi-architecture disassembly framework with Python
bindings -
PyBFD: Python interface
to the GNU Binary File Descriptor (BFD) library
Fuzzing:
-
Sulley: fuzzer development and
fuzz testing framework consisting of multiple extensible components -
Peach Fuzzing Platform:
extensible fuzzing framework for generation and mutation based
fuzzing (v2 was written in Python) -
antiparser: fuzz testing and
fault injection API -
TAOF, (The Art of Fuzzing)
including ProxyFuzz, a man-in-the-middle non-deterministic network
fuzzer - untidy: general purpose XML fuzzer
-
Powerfuzzer: highly automated and
fully customizable web fuzzer (HTTP protocol based application
fuzzer) - SMUDGE
-
Mistress:
probe file formats on the fly and protocols with malformed data,
based on pre-defined patterns -
Fuzzbox:
multi-codec media fuzzer -
Forensic Fuzzing
Tools:
generate fuzzed files, fuzzed file systems, and file systems
containing fuzzed files in order to test the robustness of forensics
tools and examination systems -
Windows IPC Fuzzing
Tools:
tools used to fuzz applications that use Windows Interprocess
Communication mechanisms -
WSBang:
perform automated security testing of SOAP based web services -
Construct: library for parsing
and building of data structures (binary or textual). Define your
data structures in a declarative manner -
fuzzer.py
(feliam):
simple fuzzer by Felipe Andres Manzano -
Fusil: Python library
used to write fuzzing programs
Web:
-
Requests: elegant and simple HTTP
library, built for human beings -
HTTPie: human-friendly cURL-like command line
HTTP client -
ProxMon:
processes proxy logs and reports discovered issues -
WSMap:
find web service endpoints and discovery files -
Twill: browse the Web from a command-line
interface. Supports automated Web testing -
Ghost.py: webkit web client written
in Python -
Windmill: web testing tool designed
to let you painlessly automate and debug your web application -
FunkLoad: functional and load web
tester -
spynner: Programmatic web
browsing module for Python with Javascript/AJAX support -
python-spidermonkey:
bridge to the Mozilla SpiderMonkey JavaScript engine; allows for the
evaluation and calling of Javascript scripts and functions -
mitmproxy: SSL-capable, intercepting HTTP
proxy. Console interface allows traffic flows to be inspected and
edited on the fly -
pathod / pathoc: pathological daemon/client
for tormenting HTTP clients and servers
取证分析:
-
Volatility:
extract digital artifacts from volatile memory (RAM) samples -
Rekall:
memory analysis framework developed by Google -
LibForensics: library for
developing digital forensics applications -
TrIDLib, identify file types
from their binary signatures. Now includes Python binding - aft: Android forensic toolkit
恶意代码分析:
-
pyew: command line hexadecimal
editor and disassembler, mainly to analyze malware -
Exefilter: filter file formats
in e-mails, web pages or files. Detects many common file formats and
can remove active content -
pyClamAV: add
virus detection capabilities to your Python software -
jsunpack-n, generic
JavaScript unpacker: emulates browser functionality to detect
exploits that target browser and browser plug-in vulnerabilities -
yara-python:
identify and classify malware samples -
phoneyc: pure Python
honeyclient implementation -
CapTipper: analyse, explore and
revive HTTP malicious traffic from PCAP file
PDF文件分析:
-
peepdf:
Python tool to analyse and explore PDF files to find out if they can be harmful -
Didier Stevens’ PDF
tools: analyse,
identify and create PDF files (includes PDFiD, pdf-parser and make-pdf and mPDF) -
Opaf: Open PDF Analysis Framework.
Converts PDF to an XML tree that can be analyzed and modified. -
Origapy: Python wrapper
for the Origami Ruby module which sanitizes PDF files -
pyPDF2: pure Python PDF toolkit: extract
info, spilt, merge, crop, encrypt, decrypt… -
PDFMiner:
extract text from PDF files -
python-poppler-qt4:
Python binding for the Poppler PDF library, including Qt4 support
杂项:
-
InlineEgg:
toolbox of classes for writing small assembly programs in Python -
Exomind:
framework for building decorated graphs and developing open-source
intelligence modules and ideas, centered on social network services,
search engines and instant messaging -
RevHosts: enumerate
virtual hosts for a given IP address -
simplejson: JSON
encoder/decoder, e.g. to use Google’s AJAX
API -
PyMangle: command line tool
and a python library used to create word lists for use with other
penetration testing tools -
Hachoir: view and
edit a binary stream field by field -
py-mangle: command line tool
and a python library used to create word lists for use with other
penetration testing tools
其他有用的扩展库与工具:
-
IPython: enhanced interactive Python
shell with many features for object introspection, system shell
access, and its own special command system -
Beautiful Soup:
HTML parser optimized for screen-scraping -
matplotlib: make 2D plots of
arrays -
Mayavi: 3D scientific
data visualization and plotting -
RTGraph3D: create
dynamic graphs in 3D - Twisted: event-driven networking engine
-
Suds: lightweight SOAP client for
consuming Web Services -
M2Crypto:
most complete OpenSSL wrapper - NetworkX: graph library (edges, nodes)
-
Pandas: library providing
high-performance, easy-to-use data structures and data analysis
tools -
pyparsing: general parsing
module -
lxml: most feature-rich and easy-to-use library
for working with XML and HTML in the Python language -
Whoosh: fast, featureful
full-text indexing and searching library implemented in pure Python -
Pexpect: control and automate
other programs, similar to Don Libes `Expect` system -
Sikuli, visual technology
to search and automate GUIs using screenshots. Scriptable in Jython -
PyQt and PySide: Python bindings for the Qt
application framework and GUI library
相关书籍:
- Violent Python by TJ O’Connor. A Cookbook for Hackers, Forensic Analysts, Penetration Testers and Security Engineers
-
Grey Hat Python by Justin Seitz:
Python Programming for Hackers and Reverse Engineers. -
Black Hat Python by Justin Seitz:
Python Programming for Hackers and Pentesters -
Python Penetration Testing Essentials by Mohit:
Employ the power of Python to get the best out of pentesting - Python for Secret Agents by Steven F. Lott. Analyze, encrypt, and uncover intelligence data using Python
其他:
- SecurityTube Python Scripting Expert (SPSE) is an online course and certification offered by Vivek Ramachandran.
- SANS offers the course SEC573: Python for Penetration Testers.
- The Python Arsenal for Reverse Engineering is a large collection of tools related to reverse engineering.
- There is a SANS paper about Python libraries helpful for forensic analysis (PDF).
- For more Python libaries, please have a look at PyPI, the Python Package Index.
密码保护:渗透测试技巧总结
【转载】34款Firefox渗透测试插件
原文地址: http://www.freebuf.com/tools/5361.html
工欲善必先利其器,firefox一直是各位渗透师必备的利器,小编这里推荐34款firefox渗透测试辅助插件,其中包含渗透测试、信息收集、代理、加密解密等功能。
1:Firebug
Firefox的 五星级强力推荐插件之一,不许要多解释
2:User Agent Switcher
改变客户端的User Agent的一款插件
3:Hackbar
攻城师必备工具,提供了SQL注入和XSS攻击,能够快速对字符串进行各种编码。
4:HttpFox
监测和分析浏览器与web服务器之间的HTTP流量
5:Live HTTP Headers
即时查看一个网站的HTTP头
6:Tamper Data
查看和修改HTTP/HTTPS头和POST参数
7:ShowIP
在状态栏显示当前页的IP地址、主机名、ISP、国家和城市等信息。
8:OSVDB
开放源码的漏洞数据库检索
9:Packet Storm search plugin
Packet Storm提供的插件,可以搜索漏洞、工具和exploits等。
10:Offsec Exploit-db Search
搜索Exploit-db信息
11:Security Focus Vulnerabilities Search Plugin
在Security Focus上搜索漏洞
12:Cookie Watcher
在状态栏显示cookie
13:Header Spy
在状态栏显示HTTP头
14:Groundspeed
Manipulate the application user interface.
15:CipherFox
在状态栏显示当前SSL/TLS的加密算法和证书
16:XSS Me
XSS测试扩展
17:SQL Inject Me
SQL注入测试扩展
18:Wappalyzer
查看网站使用的应用程序
19:Poster
发送与Web服务器交互的HTTP请求,并查看输出结果
20:Javascript Deobfuscator
显示网页上运行的Javascript代码
21:Modify Headers
修改HTTP请求头
22:FoxyProxy
代理工具
23:FlagFox
可以在地址栏或状态栏上显示出当前网站所在国家的国旗,也有更多的其他功能,如:双击国旗可以实现WOT功能;鼠标中键点击是whois功能。当然用户可以在选项里设置快捷键实现诸如复制IP,维基百科查询等功能。
24:Greasemonkey
greasemonkey 使你可以向任何网页添加DHTML语句(用户脚本)来改变它们的显示方式。就像CSS可以让你接管网页的样式,而用户脚本(User Script)则可以让你轻易地控制网页设计与交互的任何方面。例如:
* 使页面上显示的 URL 都成为可以直接点击进入的链接。
* 增强网页实用性,使你经常访问的网站更符合你的习惯。
* 绕过网站上经常出现的那些烦人的 Bug。
25:Domain Details
显示服务器类型、IP地址、域名注册信息等
26:Websecurify
Websecurify是WEB安全检测软件的Firefox的扩展,可以针对Web应用进行安全评估
27:XSSed Search
搜索XSSed.Com跨站脚本数据库
28:ViewStatePeeker
查看asp.net的iewState
29:CryptoFox
破解MD5、加密/解密工具
30:WorldIP
显示服务器的IP、地址、PING、Traceroute、RDNS等信息
31:Server Spy
识别访问的web服务器类型,版本以及IP地址的插件
32:Default Passwords
搜索CIRT.net默认密码数据库。
33:Snort IDS Rule Search
搜索Snort的IDS规则,做签名开发的应该很有用。
34:FireCAT
FireCAT (Firefox Catalog of Auditing exTensions)是一个收集最有效最有用的应用程序安全审计和风险评估工具的列表(这些工具以Firefox插件形式发布的),FireCAT中没有收集的安全工具类型包括:fuzzer,代理和应用程序扫描器.
【转载】常用渗透及入侵技巧总结
常用渗透及入侵技巧总结如下:
-
数据库备份拿shell的时候有时候不成功就备份成解析格式的试试
-
上传图片木马遇到拦截系统,连图片木马都上传不了,记事本打开图片木马在代码最前面加上gif89a试试
-
当后台有数据库备份但没有上传点时,把一句话木马插到任意处,数据库备份里备份成asp木马,再用一句话客户端连接木马
-
当网站前台有“会员注册” 注册一个账户进去看看有没有上传点,有的话直接上传asp木马以及利用iis6.0解析漏洞,不行就抓包用明小子上传
-
当页面提示只能上传jpg|gif|png等格式的时候,右键查看源文件,本地修改为asp|asa|php再本地上传即可拿下shell
-
入侵网站之前连接下3389,可以连接上的话先尝试弱口令,不行就按5次shift键,看看有没有shift后门,再尝试后门弱口令
-
访问后台地址时弹出提示框“请登陆” 把地址记出来(复制不了)放到“网页源代码分析器”里,选择浏览器-拦截跳转勾选–查看即可直接进入后台
-
ewebeditor编辑器后台增加了asp|asa|cer|php|aspx等扩展名上传时都被过滤了,就增加一个aaspsp再上传asp木马就会解析成功了
-
当注入工具猜解表段,但猜解字段时提示长度超过50之类,不妨扔到穿山甲去猜解试试,有时候就能成功猜解
-
当获得管理员密码却不知道管理员帐号时,到网站前台找新闻链接,一般“提交者”“发布者”的名字就是管理员的帐号了
-
菜刀里点击一句话木马地址右键,选择虚拟机终端,执行命令出现乱码时,返回去设置编码那里,将默认的GB2312改为UTF-8
-
破解出md5为20位,就把前3位和后1位去掉,剩余16位拿去CMD5解密就可以了
-
有时在木马代码里加上gif89a,上传成功访问的时候却出现了像图片一样的错误图像,说明服务器把gif89a当做图片来处理了,不要带gif89a就可以
-
网站的主站一般都很安全,这时就要旁注或C段了,但是想知道各个IP段开放了什么端口吗?用“啊D网络工具包”里面的IP端口扫描最明细了
-
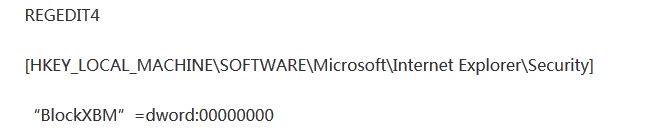
有的后台不显示验证码,往注册表里添加一个ceg即可突破这个困境了,把下面的代码保存为Code.reg,双击导入就可以了
-
旁注入侵的时候,建议挑php的站点来日,因为php站点一般都支持aspx脚本,aspx里权限比较大,对提权希望比较大呢
-
在注入点后面加上-1,若返回的页面和前面不同,是另一个正常的页面,则表示存在注入漏洞,而且是数字型的注入漏洞,在注入点后面加上-0,若返回的页面和之前的页面相同,然后加上-1,返回错误页面,则也表示存在注入漏洞,而且也是数字型的注入漏洞
-
Linux的解析格式:1.php.xxx (xxx可以是任意) 如果apache不认识后缀为rar的文件,就用1.php.rar格式上传,文件就会被服务器当做PHP脚本解析
-
辨别linux系统方法:例如:http://www.xxx.com/xxx/abc.asp?id=125 把b换成大写B访问,如果出错了,就说明是linux系统,反之是windows系统
-
如何探测服务器上哪些站点支持aspx呢? 利用bing搜索:http://cn.bing.com/ 搜索格式:ip:服务器ip aspx
-
PHP万能密码(帐号:’ UNION Select 1,1,1 FROM admin Where ”=’密码:1)
-
ASP万能密码(帐号密码均是’or’=’or’或admin’or’1=1)
-
当我们通过注入或是社工把管理员的帐号跟md5密码搞到手的时候,却发现破解不出密码 (MD5是16位加密的),那么我们就可以用COOKIE欺骗来绕过,利用桂林老兵的cookie欺骗工具,把自己的ID以及md5密码都修改成管理员的,再修改cookie,访问时就会实现欺骗了
-
倘若目标站开了cdn加速,真实地址会被隐藏起来,我们想搞它就比较困难了。
-
一般而言,后台插一句话,如果数据库扩展名是asp的话,那么插数据库,但是如果有配置文件可以插的话,那肯定是插入配置文件了,但是插 入配置文件有一个很大的风险,那就是一旦出错那么全盘皆输,有可能不仅仅造成后台无法登陆,甚至有可能是整个网站系统崩溃,所以插入配置文件,请慎之又 慎。
-
自己的03服务器系统运行burp命令:java -jar bs1407.jar
-
记得常扫inc目录,很多时候存在fck编辑器
相关链接: